Msfenum: automation of MSF auxiliary modules
wesley
 Low hanging fruit scans can be very useful when performing a penetration test. Especially when performing a internal penetration test a low hanging fruit scan can be very effective. Usually when performing a internal penetration test I am using among other things the Metasploit auxiliary modules to quickly enumerate the network. The modules can give some interesting findings very quickly, such as:
Low hanging fruit scans can be very useful when performing a penetration test. Especially when performing a internal penetration test a low hanging fruit scan can be very effective. Usually when performing a internal penetration test I am using among other things the Metasploit auxiliary modules to quickly enumerate the network. The modules can give some interesting findings very quickly, such as:
- open SMB/NFS shares;
- End-of-life systems, such as Windows XP & Windows 2003 server;
- MS17-010 vulnerable systems.
Those findings are quick wins and can give you an entry point to the network in order to escalate privileges (e.g. MS17-010 -> DA creds) pretty fast. This helps to tell your customer that you were able to obtain high network permissions within a few hours (if you are able, a malicious attacker is able as well).
Automating these steps would be useful to give us a quick initial view of a client network. Allowing us more time for more manual validation steps. Next to this we can use this to standardize some of the pentesters workflow to make sure all team members perform the same baseline checks.
Writing a tool called ‘msfenum’
Metasploit makes it pretty easy to run those auxiliary modules, however I was looking for a way to make this even faster (plug into the network and run all the modules). I was thinking about writing a tool to automate this, which only needs an IP-range to be scanned. I shared my idea with @rikvduijn, he got pretty enthusiastic about the idea. He got an idea on how to structure this tool and started writing the skeleton the same night :-).
The next day I looked into the thing that he wrote, the skeleton was a nice start to create a tiny, modular system to run those auxiliary modules automatically. So I continued on that skeleton improve it. Also one of my other collegeaus @Ag0s_, started writing some cool additions / improvements in msfenum. 🙂
Running msfenum
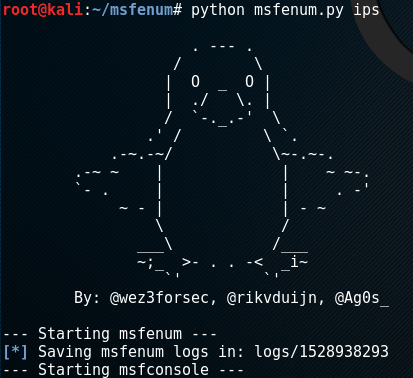
The usage of msfenum is very simple. Use a Linux system with Metasploit Framework installed, such as Kali. Clone the github page:
git clone https://github.com/wez3/msfenum
Run the command (TARGET_FILE is a file with IPs/IP-ranges line by line):
python msfenum.py TARGET_FILE -t <numberofthreads>
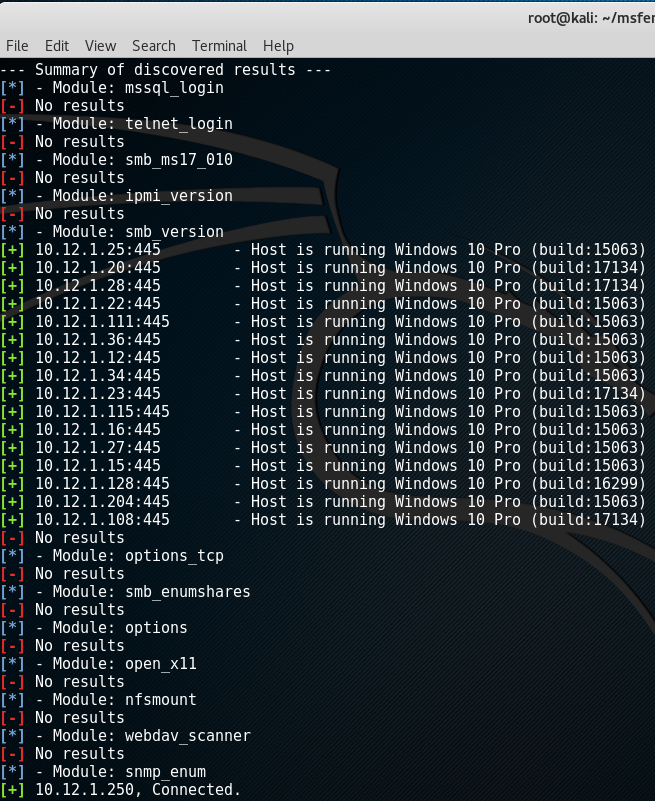
After running msfenum, all auxiliary output history is stored in the “logs/” folder in separate files per module. Also, a summary is printed by the tool after it completed:
Adding a module
A nice thing about the skeleton is that the scripts exists of a very simple structure on how to add auxiliary modules. This requires the following:
config file
There is a config file present. Here the modules you like to add can be defined in the “modules” entry.
modules folder
After adding it to the config file, a module file needs to be created in the “modules/” folder. Create a new file with the name of the modules (value after the last “/”, e.g. smb_version). Add the specific RC commands to run for your newly added module.
Contribution
That’s it. The module is added. The modules system was created in the hope, other people, with useful auxiliary scans can commit the useful scans back on the Github page. This way, we can help each other to improve (internal) penetration tests :-).
Some possible additions for the future are:
- parsing the MSF output logs to show results in a standardised way;
- new modules!